31 search results - page 6 / 7 » A Prototype Biometric Security Authentication System Based u... |
ISI
2006
Springer
13 years 6 months ago
2006
Springer
As a result of growing misuse of online anonymity, researchers have begun to create visualization tools to facilitate greater user accountability in online communities. In this stu...
WPES
2003
ACM
13 years 11 months ago
2003
ACM
We present a model and protocol for anonymous credentials. Rather than using deterrents to ensure non-transferability, our model uses secure hardware with biometric authentication...
PRL
2007
13 years 5 months ago
2007
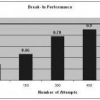
Government agencies are investing a considerable amount of resources into improving security systems as result of recent terrorist events that dangerously exposed flaws and weakn...
CIARP
2003
Springer
13 years 11 months ago
2003
Springer
Most people are used to signing documents and because of this, it is a trusted and natural method for user identity verification, reducing the cost of password maintenance and decr...
ICPR
2006
IEEE
14 years 7 months ago
2006
IEEE
Regeneration of biometric templates from match scores has security and privacy implications related to any biometric based authentication system. In this paper, we propose a novel...