29 search results - page 6 / 6 » A framework for block-based timing sensitivity analysis |
IPPS
2007
IEEE
13 years 11 months ago
2007
IEEE
The vulnerable air interface, device level constraints, and insecure encryption techniques of wireless networks have naturally increased the chance of attacker obtaining users inf...
CVPR
2000
IEEE
14 years 7 months ago
2000
IEEE
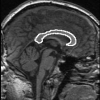
In this paper, we present a novel approach to robust skeleton extraction. We use undirected graphs to model connectivity of the skeleton points. The graph topology remains unchang...
VC
2010
12 years 11 months ago
2010
Abstract Recently proposed edge-preserving multiscale image decompositions enable artifact-free and visually appealing image editing. As the human eye is sensitive to contrast, per...
ICSM
2008
IEEE
13 years 11 months ago
2008
IEEE
Up-to-date comments are critical for the successful evolution of a software application. When modifying a function, developers may update the comment associated with the function ...