476 search results - page 3 / 96 » Analysis of signature change patterns |
SPIN
2009
Springer
13 years 11 months ago
2009
Springer
: Most intrusion detection systems deployed today apply misuse detection as analysis method. Misuse detection searches for attack traces in the recorded audit data using predefined...
ISBI
2006
IEEE
14 years 6 months ago
2006
IEEE
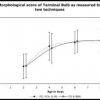
We are studying the genetic influence on rates of age related muscle degeneration in C. elegans. For this, we built pattern recognition tools to calculate a morphological score gi...
DELTA
2008
IEEE
13 years 11 months ago
2008
IEEE
Re-using embedded resources for implementing builtin self test mechanisms allows test cost reduction. In this paper we demonstrate how to implement costefficient built-in self tes...
CIC
2004
13 years 6 months ago
2004
With a better understanding of how probe packets and cross-traffic packets interact with each other, more accurate measurement methods based on active probing can be developed. Sev...
IBPRIA
2007
Springer
13 years 11 months ago
2007
Springer
Abstract. In this article, scale and orientation invariant object detection is performed by matching intensity level histograms. Unlike other global measurement methods, the presen...