348 search results - page 3 / 70 » Secure Computation on the Web: Computing without Simultaneou... |
CNIS
2006
13 years 6 months ago
2006
We present the design and a prototype of a lab course on computer security, the necessity of which arises from the students' need to complement course work by hands-on experi...
CSE
2009
IEEE
14 years 4 days ago
2009
IEEE
—The success of a Public Key Infrastructure such as the Web of Trust (WoT) heavily depends on its ability to ensure that public keys are used by their legitimate owners, thereby ...
EGC
2005
Springer
13 years 11 months ago
2005
Springer
Abstract. There are many potential users and uses for grid computing. However, the concept of sharing computing resources excites security concerns and, whilst being powerful and f...
CVPR
2010
IEEE
13 years 7 months ago
2010
IEEE
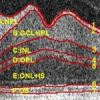
Multiple surface searching with only image intensity information is a difficult job in the presence of high noise and weak edges. We present in this paper a novel method for global...
CVPR
2012
IEEE
11 years 7 months ago
2012
IEEE
Head pose estimation is a critical problem in many computer vision applications. These include human computer interaction, video surveillance, face and expression recognition. In ...