ESA
2009
Springer
13 years 11 months ago
2009
Springer
A hash function h, i.e., a function from the set U of all keys to the range range [m] = {0, . . . , m − 1} is called a perfect hash function (PHF) for a subset S ⊆ U of size n ...
CRYPTO
2009
Springer
13 years 11 months ago
2009
Springer
RSA-FDH and many other schemes secure in the Random-Oracle Model (ROM) require a hash function with output size larger than standard sizes. We show that the random-oracle instanti...
ASIACRYPT
2009
Springer
13 years 11 months ago
2009
Springer
The design of cryptographic hash functions is a very complex and failure-prone process. For this reason, this paper puts forward a completely modular and fault-tolerant approach to...
IEEEIAS
2009
IEEE
13 years 11 months ago
2009
IEEE
: An algorithm for one-way hash function construction based on conservative chaotic system is proposed. The plaintext is divided into a group of message blocks by a fixed length an...
IEEEIAS
2009
IEEE
13 years 11 months ago
2009
IEEE
: In this paper, a hash function construction method based on cell neural network (CNN) with hyper-chaos characteristics is proposed. The chaos sequence is generated by iterating C...
AFRICACRYPT
2009
Springer
13 years 11 months ago
2009
Springer
Vortex is a hash function that was first presented at ISC’2008, then submitted to the NIST SHA-3 competition after some modifications. This paper describes several attacks on b...
CTRSA
2010
Springer
13 years 11 months ago
2010
Springer
Abstract. The TLS and SSL protocols are widely used to ensure secure communication over an untrusted network. Therein, a client and server first engage in the so-called handshake ...
CVPR
2010
IEEE
14 years 28 days ago
2010
IEEE
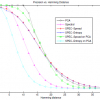
Searching approximate nearest neighbors in large scale high dimensional data set has been a challenging problem. This paper presents a novel and fast algorithm for learning binary...
FSE
2009
Springer
14 years 5 months ago
2009
Springer
Enhanced Target Collision Resistance (eTCR) property for a hash function was put forth by Halevi and Krawczyk in Crypto 2006, in conjunction with the randomized hashing mode that i...