6195 search results - page 1174 / 1239 » Cloud Computing Security |
143
click to vote
ACISP
2009
Springer
15 years 11 months ago
2009
Springer
Bernstein’s CubeHash is a hash function family that includes four functions submitted to the NIST Hash Competition. A CubeHash function is parametrized by a number of rounds r, a...
130
click to vote
AGENTS
1997
Springer
15 years 8 months ago
1997
Springer
The Robot World Cup Initiative (RoboCup) is an attempt to foster AI and intelligent robotics research by providing a standard problem where wide range of technologies can be integ...
135
click to vote
ICPR
2006
IEEE
16 years 5 months ago
2006
IEEE
Regeneration of biometric templates from match scores has security and privacy implications related to any biometric based authentication system. In this paper, we propose a novel...
115
click to vote
WWW
2002
ACM
16 years 5 months ago
2002
ACM
It is widely recognized that distributed denial-of-service (DDoS) attacks can disrupt electronic commerce and cause large revenue losses. However, effective defenses continue to b...
126
click to vote
CHI
2009
ACM
16 years 5 months ago
2009
ACM
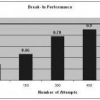
In this paper, we describe progress in research designed to explore the effect of the combination of avatars' visual fidelity and users' anticipated future interaction o...