1628 search results - page 221 / 326 » Compiler Construction Using Scheme |
150
click to vote
ACISP
2005
Springer
15 years 10 months ago
2005
Springer
We present the first group signature scheme with provable security and signature size O(λ) bits where the group manager, the group members, and the Open Authority (OA) are all id...
157
click to vote
ECML
2003
Springer
15 years 10 months ago
2003
Springer
Abstract. Tree induction methods and linear models are popular techniques for supervised learning tasks, both for the prediction of nominal classes and continuous numeric values. F...
129
click to vote
SPW
2004
Springer
15 years 10 months ago
2004
Springer
This note presents a new way of composing cryptographic primitives which makes some novel combinations possible. For example, one can do threshold decryption using standard block c...
168
click to vote
CVPR
2008
IEEE
16 years 6 months ago
2008
IEEE
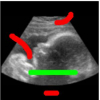
We propose a scheme to introduce directionality in the Random Walker algorithm for image segmentation. In particular, we extend the optimization framework of this algorithm to com...
162
click to vote
WD
2010
15 years 2 months ago
2010
In this paper we propose a distributed approach to construct vicinity resource maps at each node in a delaytolerant network. The scheme uses recent encounters to estimate the avail...