7623 search results - page 198 / 1525 » Constructive Volume Modeling |
125
Voted
ACISP
2006
Springer
15 years 7 months ago
2006
Springer
The only known construction of identity-based signatures that can be proven secure in the standard model is based on the approach of attaching certificates to non-identity-based si...
109
Voted
SPAA
1998
ACM
15 years 8 months ago
1998
ACM
We present a computation-centric theory of memory models. Unlike traditional processor-centric models, computation-centric models focus on the logical dependencies among instructi...
317
Voted
Presentation
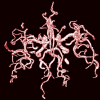
In this paper, we present an automatic statistical approach for extracting 3D blood vessels from time-of-flight (TOF) magnetic resonance angiography (MRA) data. The voxels of the d...
139
Voted
ICPP
2000
IEEE
15 years 8 months ago
2000
IEEE
Current VLSI technology allows more than two wiring layers and the number is expected to rise in future. In this paper, we show that, by designing VLSI layouts directly for an L-l...
117
Voted
ENGL
2008
15 years 3 months ago
2008
A numerical scheme for bubble trajectories including their collisions is developed. An Eulerian-Lagrangian computational scheme is used to study the bubble trajectories. The 2D ave...