533 search results - page 93 / 107 » Control flow based obfuscation |
180
click to vote
FORMATS
2007
Springer
15 years 9 months ago
2007
Springer
Abstract. We describe a partial order reduction technique for a realtime component model. Components are described as timed automata with data ports, which can be composed in stati...
150
click to vote
GLOBECOM
2007
IEEE
15 years 9 months ago
2007
IEEE
Abstract-- The emerging high-rate wireless personal area network (WPAN) technology is capable of supporting high-speed and high-quality real-time multimedia applications. In partic...
168
click to vote
ESORICS
2000
Springer
15 years 9 months ago
2000
Springer
Several authors have proposed using code modification as a technique for enforcing security policies such as resource limits, access controls, and network information flows. Howeve...
301
click to vote
CVPR
2010
IEEE
15 years 7 months ago
2010
IEEE
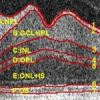
Multiple surface searching with only image intensity information is a difficult job in the presence of high noise and weak edges. We present in this paper a novel method for global...
140
click to vote
EDOC
2008
IEEE
15 years 7 months ago
2008
IEEE
The service-oriented architectural style is widely perceived today. However, service orientation is a very general concept and its application in real-life situations is somewhat ...