3276 search results - page 356 / 656 » Data Management for Pervasive Computing |
164
Voted
CYBERC
2011
14 years 3 months ago
2011
— Cloud computing is gaining tremendous momentum in both academia and industry. The application of Cloud computing, however, has mostly focused on Web applications and business a...
257
click to vote
Publication
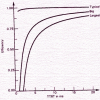
The performance of Fiber-Distributed Data Interface (FDDI) depends upon several workload parameters; for example; the arrival pattern, frame size, and configuration parameters, suc...
132
Voted
APSCC
2008
IEEE
15 years 10 months ago
2008
IEEE
— We discuss a learning model that enables the creation of optimal learning strategies that suit learners’ needs. A customized learning content is delivered to learners as mana...
135
click to vote
ICDCSW
2007
IEEE
15 years 10 months ago
2007
IEEE
Distributed Hash Tables (DHT) was not designed to be secure against malicious users. But some secure systems like trust and reputation management algorithms trust DHT with their d...
144
click to vote
GI
2005
Springer
15 years 9 months ago
2005
Springer
: Radio Frequency Identification (RFID) technology has a lot of potential to bridge the gap between the virtual world of enterprise IT systems and the real world of products and l...