642 search results - page 93 / 129 » Detecting Spoofed Packets |
176
click to vote
JSAC
2006
15 years 4 months ago
2006
Abstract-- As mobile ad hoc network applications are deployed, security emerges as a central requirement. In this paper, we introduce the wormhole attack, a severe attack in ad hoc...
182
Voted
NOSSDAV
2010
Springer
15 years 9 months ago
2010
Springer
Real-time Transport Protocol (RTP) is a widely adopted standard for transmission of multimedia traffic in Internet telephony (commonly known as VoIP). Therefore, it is a hot poten...
255
Voted
Publication
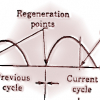
We propose a scheme for congestion avoidance in networks using a connectionless protocol at the network layer. The scheme uses a minimal amount of feedback from the network to the ...
163
Voted
INFOCOM
2008
IEEE
15 years 11 months ago
2008
IEEE
Abstract— This paper experimentally investigates the feasibility of crypto-free communications in resource-constrained wireless sensor networks. We exploit the spatial signature ...
123
Voted
BROADNETS
2007
IEEE
15 years 11 months ago
2007
IEEE
—Failure recovery in IP networks is critical to high quality service provisioning. The main challenge is how to achieve fast recovery without introducing high complexity and reso...