4553 search results - page 679 / 911 » Distributed Ranked Search |
109
Voted
SIGSOFT
2005
ACM
16 years 4 months ago
2005
ACM
Before performing a modification task, a developer usually has to investigate the source code of a system to understand how to carry out the task. Discovering the code relevant to...
164
click to vote
SIGSOFT
2003
ACM
16 years 4 months ago
2003
ACM
Writes via unchecked pointer dereferences rank high among vulnerabilities most often exploited by malicious code. The most common attacks use an unchecked string copy to cause a b...
108
Voted
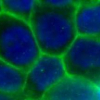
ISBI
2008
IEEE
16 years 4 months ago
2008
IEEE
Cell membrane proteins play an important role in tissue architecture and cell-cell communication. We hypothesize that segmentation and multivariate characterization of the distrib...
107
Voted
WWW
2007
ACM
16 years 4 months ago
2007
ACM
Major research challenges in discovering Web services include, provisioning of services across multiple or heterogeneous registries, differentiating between services that share si...
147
Voted
KDD
2007
ACM
16 years 3 months ago
2007
ACM
To unravel the concept structure and dynamics of the bioinformatics field, we analyze a set of 7401 publications from the Web of Science and MEDLINE databases, publication years 1...