7228 search results - page 138 / 1446 » From Algorithmic to Subjective Randomness |
128
Voted
INFOCOM
2010
IEEE
15 years 2 months ago
2010
IEEE
—Network Tomography (or network monitoring) uses end-to-end path-level measurements to characterize the network, such as topology estimation and failure detection. This work prov...
144
Voted
ICCV
2011
IEEE
14 years 3 months ago
2011
IEEE
Drawing a box around an intended segmentation target has become both a popular user interface and a common output for learning-driven detection algorithms. Despite the ubiquity of...
316
click to vote
Presentation
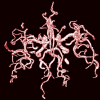
In this paper, we present an automatic statistical approach for extracting 3D blood vessels from time-of-flight (TOF) magnetic resonance angiography (MRA) data. The voxels of the d...
116
click to vote
HICSS
2009
IEEE
15 years 10 months ago
2009
IEEE
Privacy preserving data mining has been investigated extensively. The previous works mainly fall into two categories, perturbation and randomization based approaches and secure mu...
166
click to vote
ALGORITHMICA
2006
15 years 3 months ago
2006
Dai, Li, and Wu proposed Rule k, a localized approximation algorithm that attempts to find a small connected dominating set in a graph. In this paper we consider the "average...