2916 search results - page 460 / 584 » Generating Rule Sets from Model Trees |
157
click to vote
AVBPA
2005
Springer
15 years 10 months ago
2005
Springer
Most of the prior work in biometric literature has only emphasized on the issue of feature extraction and classification. However, the critical issue of examining the usefulness of...
135
click to vote
SPLC
2008
15 years 5 months ago
2008
Software Product-lines (SPLs) use modular software components that can be reconfigured into different variants for different requirements sets. Feature modeling is a common method...
174
click to vote
QEST
2009
IEEE
15 years 11 months ago
2009
IEEE
—Traviando is a trace analyzer and visualizer for simulation traces of discrete event dynamic systems. In this paper, we briefly outline recent extensions of Traviando towards a...
164
click to vote
VIS
2003
IEEE
16 years 5 months ago
2003
IEEE
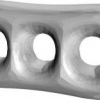
We present a new algorithm for simplifying the shape of 3D objects by manipulating their medial axis transform (MAT). From an unorganized set of boundary points, our algorithm com...
141
click to vote
ACNS
2007
Springer
15 years 10 months ago
2007
Springer
In a proxy re-encryption scheme a semi-trusted proxy converts a ciphertext for Alice into a ciphertext for Bob without seeing the underlying plaintext. A number of solutions have ...