16070 search results - page 21 / 3214 » Identifying |
129
click to vote
RE
2007
Springer
15 years 4 months ago
2007
Springer
This paper describes the use of Obstacle Analysis to identify anomaly handling requirements for a safety-critical, autonomous system. The software requirements for the system evolv...
161
click to vote
SPIRE
2010
Springer
15 years 2 months ago
2010
Springer
Next generation sequencing (NGS) technologies are being applied to many fields of biology, notably to survey the polymorphism across individuals of a species. However, while single...
164
click to vote
CSMR
2010
IEEE
14 years 12 months ago
2010
IEEE
Abstract--Concept or feature identification, i.e., the identification of the source code fragments implementing a particular feature, is a crucial task during software understandin...
276
click to vote
PERVASIVE
2011
Springer
14 years 7 months ago
2011
Springer
People spend most of their time at a few key locations, such as home and work. Being able to identify how the movements of people cluster around these “important places” is cru...
300
click to vote
ICDE
2009
IEEE
17 years 4 months ago
2009
IEEE
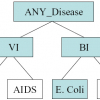
Existing approaches on privacy-preserving data publishing rely on the assumption that data can be divided into quasi-identifier attributes (QI) and sensitive attribute (SA). This ...