1813 search results - page 310 / 363 » Instance Pruning Techniques |
105
click to vote
VIS
2005
IEEE
16 years 1 months ago
2005
IEEE
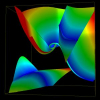
Tensor topology is useful in providing a simplified and yet detailed representation of a tensor field. Recently the field of 3D tensor topology is advanced by the discovery that d...
DAC
2000
ACM
16 years 26 days ago
2000
ACM
Recently, intellectual property protection (IPP) techniques attracted a great deal of attention from semiconductor, system integration and software companies. A number of watermar...
107
click to vote
WWW
2004
ACM
16 years 17 days ago
2004
ACM
The ability to accurately identify the network traffic associated with different P2P applications is important to a broad range of network operations including application-specifi...
TCC
2009
Springer
16 years 13 days ago
2009
Springer
The concept of witness-hiding suggested by Feige and Shamir is a natural relaxation of zero-knowledge. In this paper we identify languages and distributions for which many known co...
109
click to vote
KDD
2006
ACM
16 years 8 days ago
2006
ACM
The problem of assessing the significance of data mining results on high-dimensional 0?1 data sets has been studied extensively in the literature. For problems such as mining freq...