1689 search results - page 258 / 338 » Modelling Devices for Natural Interaction |
123
click to vote
INFOCOM
2010
IEEE
15 years 2 months ago
2010
IEEE
Abstract—The widespread availability of mobile wireless devices offers growing opportunities for the formation of temporary networks with only intermittent connectivity. These in...
165
click to vote
CORR
2010
Springer
14 years 11 months ago
2010
Springer
Push message delivery, where a client maintains an "always-on" connection with a server in order to be notified of a (asynchronous) message arrival in real-time, is incre...
136
click to vote
ICSE
2007
IEEE-ACM
16 years 4 months ago
2007
IEEE-ACM
Abstract. In this chapter we discuss the susceptibility of critical information infrastructures to computer-borne attacks and faults, mainly due to their largely computerized natur...
149
click to vote
ICCV
2007
IEEE
16 years 6 months ago
2007
IEEE
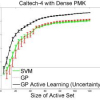
Discriminative methods for visual object category recognition are typically non-probabilistic, predicting class labels but not directly providing an estimate of uncertainty. Gauss...
147
click to vote
RECSYS
2009
ACM
15 years 10 months ago
2009
ACM
Current conversational recommender systems are unable to offer guarantees on the quality of their recommendations due to a lack of principled user utility models. We develop an ap...