7587 search results - page 128 / 1518 » Network Analysis and Visualisation |
113
click to vote
ISI
2004
Springer
15 years 9 months ago
2004
Springer
Malicious insiders’ difficult-to-detect activities pose serious threats to the intelligence community (IC) when these activities go undetected. A novel approach that integrates ...
263
click to vote
Publication
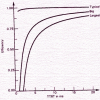
The performance of Fiber-Distributed Data Interface (FDDI) depends upon several workload parameters; for example; the arrival pattern, frame size, and configuration parameters, suc...
145
click to vote
HICSS
2007
IEEE
15 years 10 months ago
2007
IEEE
Most network anomaly detection research is based on packet header fields, while the payload is usually discarded. Preventing unknown attacks and Internet worms has led to a need f...
124
click to vote
AINA
2007
IEEE
15 years 10 months ago
2007
IEEE
In this paper, we study the adequacy of applying peer-topeer techniques to mobile networks by conducting a series of experiments using smart phones as peers. We measure important ...
125
click to vote
ICMCS
2006
IEEE
15 years 10 months ago
2006
IEEE
In this paper, we propose an accurate analytical model to analyze the performance of initial ranging requests in IEEE 802.16 networks. Two metrics, connection probability and aver...