2187 search results - page 189 / 438 » Performance analysis of distributed embedded systems |
155
click to vote
SRDS
1999
IEEE
15 years 8 months ago
1999
IEEE
Hybrid systems like computer-controlled chemical plants are typical safety critical distributed systems. In present practice, the safety of hybrid systems is guaranteed by hazard ...
162
click to vote
TMC
2008
15 years 4 months ago
2008
There is a vast literature on the throughput analysis of the IEEE 802.11 media access control (MAC) protocol. However, very little has been done on investigating the interplay betw...
159
click to vote
CCGRID
2006
IEEE
15 years 10 months ago
2006
IEEE
Component-based software construction is widely used in a variety of applications, from embedded environments to grid computing. However, errors in these applications and systems ...
146
click to vote
SIGOPS
2010
15 years 2 months ago
2010
Despite advances in the application of automated statistical and machine learning techniques to system log and trace data there will always be a need for human analysis of machine...
137
click to vote
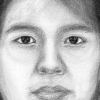
CVPR
2005
IEEE
16 years 6 months ago
2005
IEEE
Most face recognition systems focus on photo-based face recognition. In this paper, we present a face recognition system based on face sketches. The proposed system contains two e...