1050 search results - page 22 / 210 » Two methods of authenticated positioning |
130
click to vote
IJMI
2008
15 years 3 months ago
2008
Purpose: To investigate the effects of a fully functional electronic patient record (EPR) system on clinicians' work during team conferences, ward rounds, and nursing handove...
119
click to vote
ICIAP
1999
ACM
15 years 7 months ago
1999
ACM
In this paper, we applied local warping techniques to construct a frame work of image-based morphing for facial expressions animation with low complexity. From the experience we o...
113
click to vote
ICPR
2008
IEEE
16 years 4 months ago
2008
IEEE
Cancelable biometric systems are gaining in popularity for use in person authentication for applications where the privacy and security of biometric templates are important consid...
155
click to vote
TSMC
2010
14 years 9 months ago
2010
Most existing camera placement algorithms focus on coverage and/or visibility analysis, which ensures that the object of interest is visible in the camera's field of view (FOV...
125
click to vote
ISCC
2008
IEEE
15 years 9 months ago
2008
IEEE
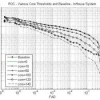
Determining where a given sensor is physically located is a challenging issue. In this paper, we address the localization problem where, initially, a certain number of sensors cal...