CODASPY
2014
11 years 12 months ago
2014
The Group-centric Secure Information Sharing (g-SIS) family of models has been proposed for modeling environments in which group dynamics dictate information-sharing policies and ...
161
click to vote
CHI
2014
ACM
11 years 12 months ago
2014
ACM
Through our art project, Metaphone, we explored a particular form of aesthetics referred to in the arts tradition as machine aesthetics. The Metaphone machine collects the partici...
CBDAR
2014
11 years 12 months ago
2014
—We show how to exploit temporal and spatial coherence to achieve efficient and effective text detection and decoding for a sensor suite moving through an environment in which t...
ACSC
2014
IEEE
11 years 12 months ago
2014
IEEE
The mixed database workloads generated by enterprise applications can be categorized into shortrunning transactional as well as long-running analytical queries with resource-inten...
56
Voted
ACE
2014
11 years 12 months ago
2014
There is a call for change in the treatment of ICT curriculum in our schools driven by the relatively recent acknowledgement of the growing importance of ICT in industry and socie...
293
click to vote
Publication
Regression-based techniques have shown promising results for people counting in crowded scenes. However, most existing techniques require expensive and laborious data annotation fo...
323
click to vote
Publication
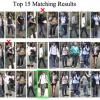
Owing to visual ambiguities and disparities, person re-identification methods inevitably produce suboptimal rank-list, which still requires exhaustive human eyeballing to identify ...
354
click to vote
Publication
Generating coherent synopsis for surveillance video stream remains a formidable challenge due to the ambiguity and uncertainty inherent to visual observations. In contrast to exist...
411
click to vote
Publication
While clustering is usually an unsupervised operation, there are circumstances in which we have prior belief that pairs of samples should (or should not) be assigned to the same cl...